What if hackers manage to hack your email account and access your computer despite your Windows Defender and Firewall are turned on, despite the two-factor authentication is enabled on your email Account? Do you know that you are the one who provides a secret path to hackers to access your computer?
Everyone of you must have got a warning from Windows while installing a software developed by an Unknown Publisher like “Do you want to install a software from an unknown publisher in your computer?” Interestingly most of you install that software despite Windows warning.
These software (not all) from unknown publishers install rootkits like CandyOpen, which are installed secretly on Windows System32 directory. A rootkit allows hackers to maintain command and control over a computer without the computer administrator knowing about it.
You must have watched the Hollywood blockbuster movie Troy, how enemy attacked the fort by hiding itself inside the Trojan Horse which was sent as a gift. Similarly these software from unknown publishers give secret path to hackers.
Mostly hackers access your email account via your computer when you are already signed-in. When they try to change or rest the password, you get email notification and SMS on your phone like “Someone is trying to change the password of your email account” or “Suspicious activity Detected”.
After visiting your emails and Google drive often hackers change the language of your email account hinting you that your email account has been hacked. If they find important information, document or file they ask you for ransom as well.
Following topics will be covered in this post:
- How To Permanently Protect Your Computer From Hacking
- How To Find The Hacker’s Location From Your Gmail Account
01. How To Protect Your Computer
Do you know that your Windows 10 comes with a builtin feature called Reputation-based protection? These are the settings which protect your computer from malicious or potentially unwanted apps, files, and websites.
Below I have shown that how this feature found a rootkit “CandyOpen” and blocked its access, after it was enabled.
Follow these steps to enable Reputation-based protection:
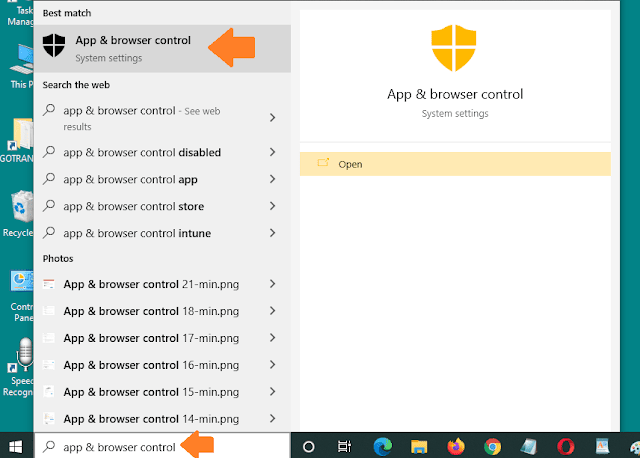
- Type app & browser control on Windows Search Bar.
- Click on the App & browser control.
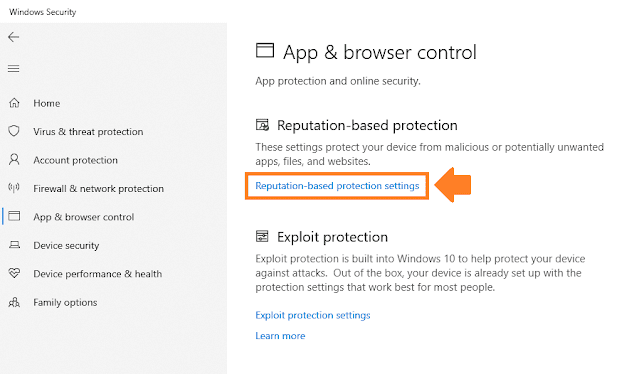
- Click on the “Reputation-based protection settings“.
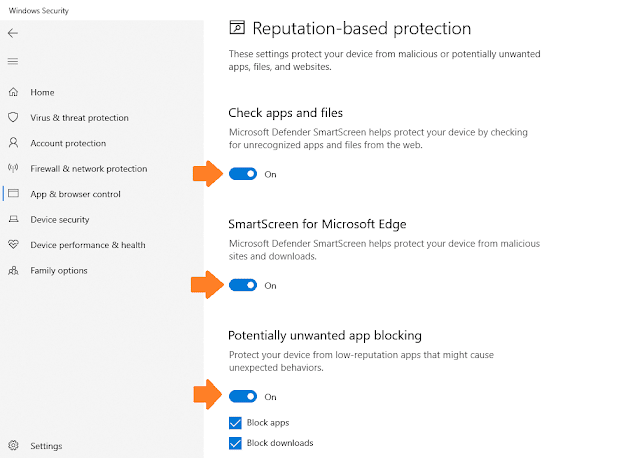
- Turn on the Check apps and files.
- Turn on SmartScreen for Microsoft Edge.
- Turn on Potentially unwanted app blocking.
- Turn on SmartScreen For Microsoft Store apps. You have successfully enabled Reputation-based protection.
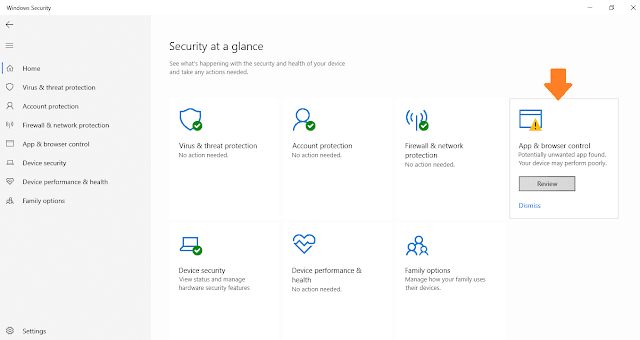
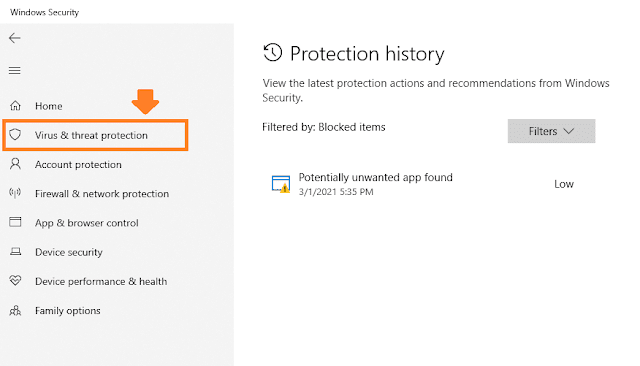
- Now go back to “Home” tab of “Windows Security” and check whether potentially unwanted app is found or not.
- Here you can see that in “App & browser control” it has found a potentially unwanted app.
- Click on “Review” to see the details.
- Click on the “Virus & threat protection” to see details about the threat.
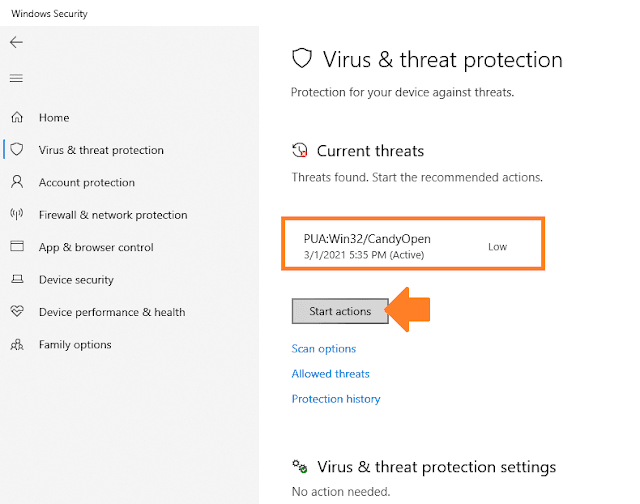
- Here you can see the details about the threat. Its name is “CandyOpen” stored in Win32. The CandyOpen is a rootkit.
- Click on the Start actions button.
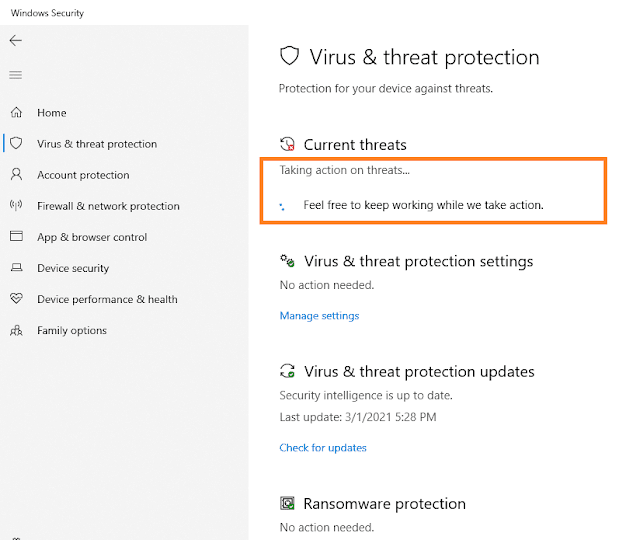
- Windows Defender will start taking the action.
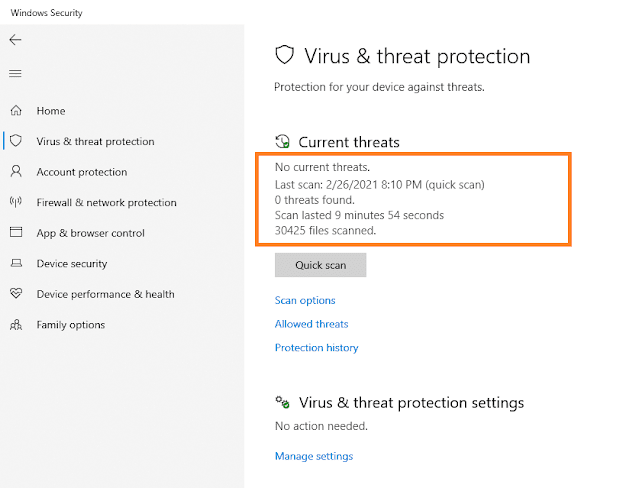
- Here you can see that there is no threat. It has also removed the software from computer through which it was installed.
- In the next section I will show you from where a hacker was trying to change the password of Gmail account.
How To Find Hacker’s Location
Above you saw how to find the threat which was used by a hacker to access the computer and email account, now let’s see how you can find the location of hacker from your Gmail account.
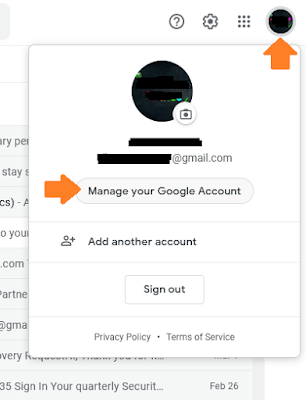
- Sign-in to your Gmail account.
- Click on your Gmail thumbnail located at top-right corner.
- Click on the “Manage your Google Account“.
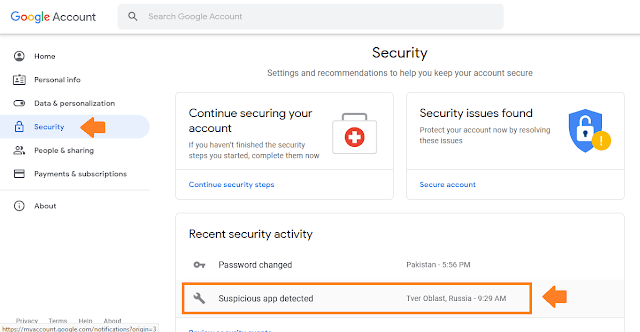
- Click on the “Security” tab.
- Here you can see under the “Recent Security activity” section that the location of hacker is “Tver Oblast, Russia”. He tried to hack Gmail account at 9:29 AM.
- Your Gmail Account offers plenty of options to secure your account. Go through those security settings and enable all the features to make your account secure.
Here are some more tips to secure your email accounts.
- Don’t signup to unknown apps and websites with your email ID.
- People often use their original password when they sign-up to apps and websites. Avoid using your original password.
- If two-factor authentication is enabled on your email account then don’t give your mobile phone to people. If someone knows your email ID he can make an attempt to change your password by sending the verification code to your mobile phone.
So it was all about protecting your computer and email account from unauthorized access. Always take care of your security. If you like this post then don’t forget to share with other people. Share your feedback in the comments section below.

Also Read
- Download Best Free iPhone Cleaner To Free Up Space Of Your iOS Device | iPhone, iPad, iPod
- Download Best iOS Data Backup & Restore Tool | Best Alternative To iTunes
- Download Best iTunes Repair Tool For Windows | Fix 100+ iTunes Errors
- Download Best Android OS Repair Tool For Windows | Samsung Galaxy, Verizon, Sprint, T-Mobile, Vodafone etc
- Download Best Android Data Recovery Tool For Windows | Google Backup, WhatsApp, Photos




Leave a Reply